
![Cloud Computing And Virtualization: A Comprehensive Overview [Presentation] 2 Cloud Computing And Virtualization Overview](https://cioindex.com/wp-content/uploads/2023/03/Cloud-Computing-and-Virtualization-Overview.jpg)







The IT Operations Editor’s Choice category in our CIO Reference Library focuses on providing IT executives, decision-makers, and professionals with a carefully curated collection of articles, resources, and expert opinions on IT operations management, best practices, and emerging trends. This category aims to showcase the most insightful and valuable content handpicked by our editorial team, enabling you to optimize and streamline your organization’s IT strategy and operations effectively.
Resources in this category will cover a variety of topics, including:
- IT Operations Management: Discover our editorial team’s top picks for articles, interviews, and expert opinions on IT operations management frameworks and methodologies, such as ITIL, DevOps, and Agile approaches.
- IT Infrastructure and Monitoring: Explore our editors’ choice for the latest tools, technologies, and techniques for managing and monitoring IT infrastructure, including network, server, storage, and cloud resources.
- IT Service Management (ITSM): Uncover the editorial team’s selection of insights from industry experts on ITSM principles, processes, and tools for delivering high-quality IT services, as well as updates on ITSM frameworks like ITIL, COBIT, and ISO/IEC 20000.
- IT Security and Compliance: Stay informed with our editor’s choice of feature articles and expert opinions on best practices and strategies for ensuring IT operations security, privacy, and compliance, including data protection, risk management, and regulatory compliance.
- IT Automation and Orchestration: Gain insights from our editorial team’s top picks on in-depth articles and interviews about IT automation and orchestration solutions, tools, and platforms for automating IT processes, workflows, and infrastructure management.
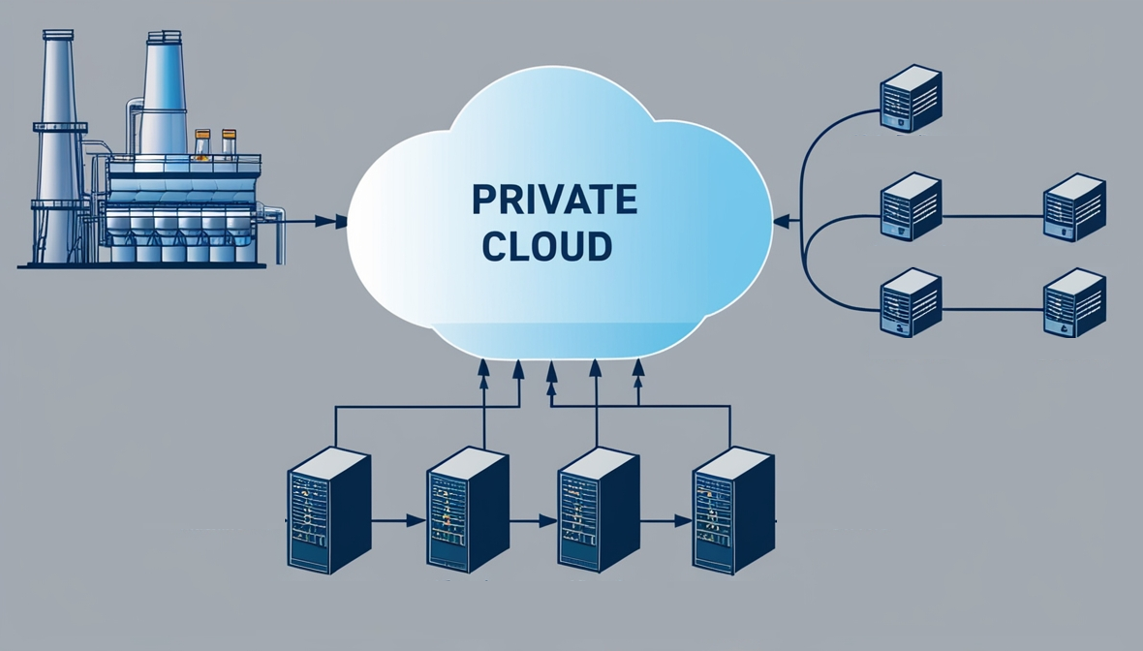
- Cloud Computing and Virtualization: Keep up with the latest insights and perspectives on cloud computing and virtualization, handpicked by our editorial team to understand their impact on IT operations management.
- IT Operations Analytics: Follow our editor’s choice of feature articles and expert opinions on the role of data analytics in IT operations, including techniques for collecting, analyzing, and visualizing IT operations data to support decision-making and continuous improvement.
- IT Cost Optimization: Stay informed about expert insights and perspectives on strategies and best practices for optimizing IT costs, handpicked by our editorial team, including techniques for analyzing IT expenditures, identifying cost-saving opportunities, and implementing cost-effective IT solutions.
- IT Service Continuity and Disaster Recovery: Keep updated on our editor’s choice of expert opinions and in-depth articles regarding IT service continuity and effective disaster recovery planning, including business continuity management and IT resilience strategies.
- IT Operations Case Studies and Success Stories: Learn from real-world feature articles and interviews about organizations that have successfully optimized and streamlined their IT operations, handpicked by our editorial team to provide insights into their strategies, challenges, and lessons learned.
The IT Operations Editor’s Choice category is designed to provide IT executives and professionals with a curated collection of the most insightful and valuable content in IT operations management. By offering a comprehensive collection of articles, resources, and expert opinions handpicked by our editorial team, this category seeks to support informed decision-making and strategic planning in IT operations and service delivery.